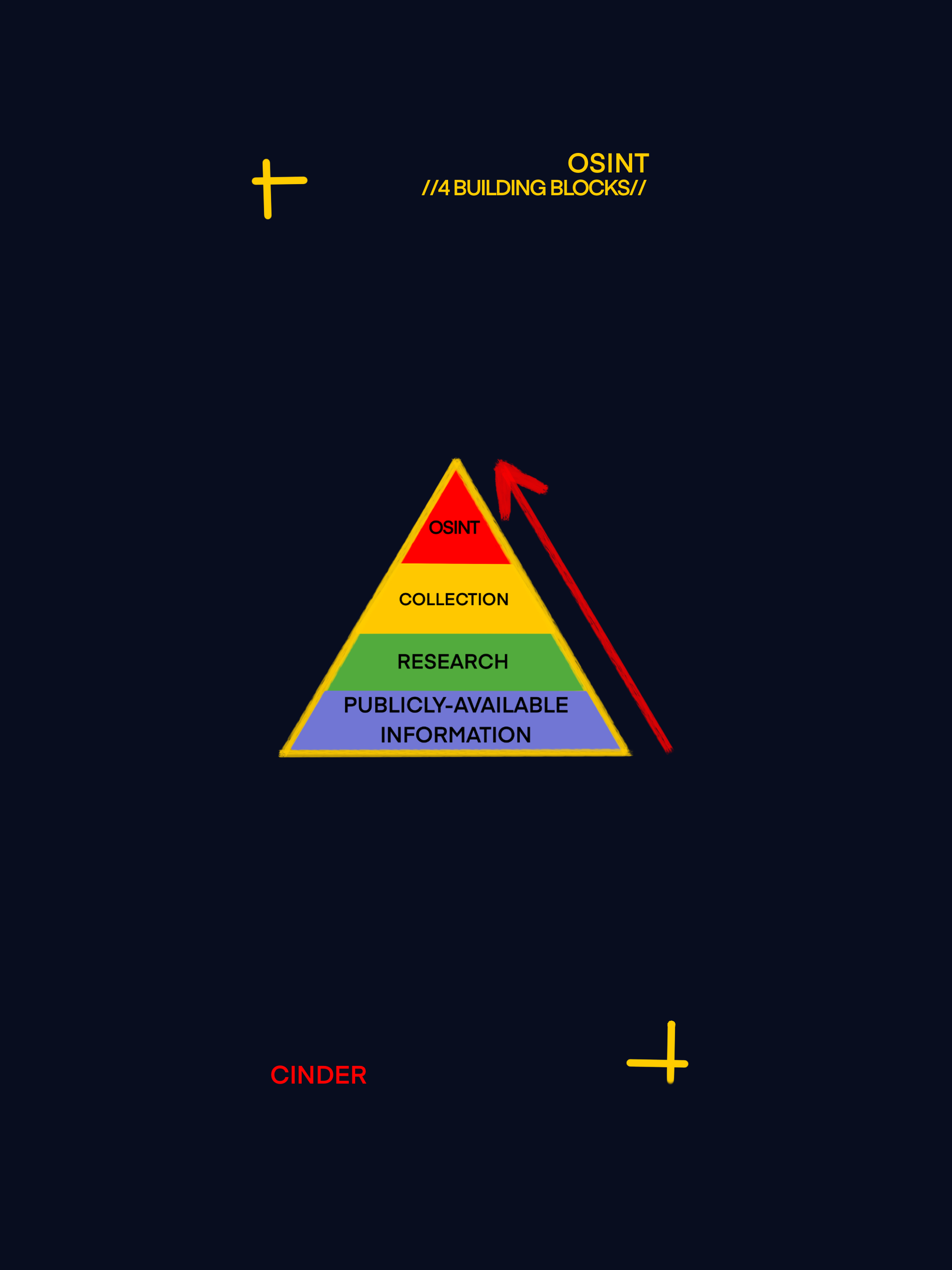
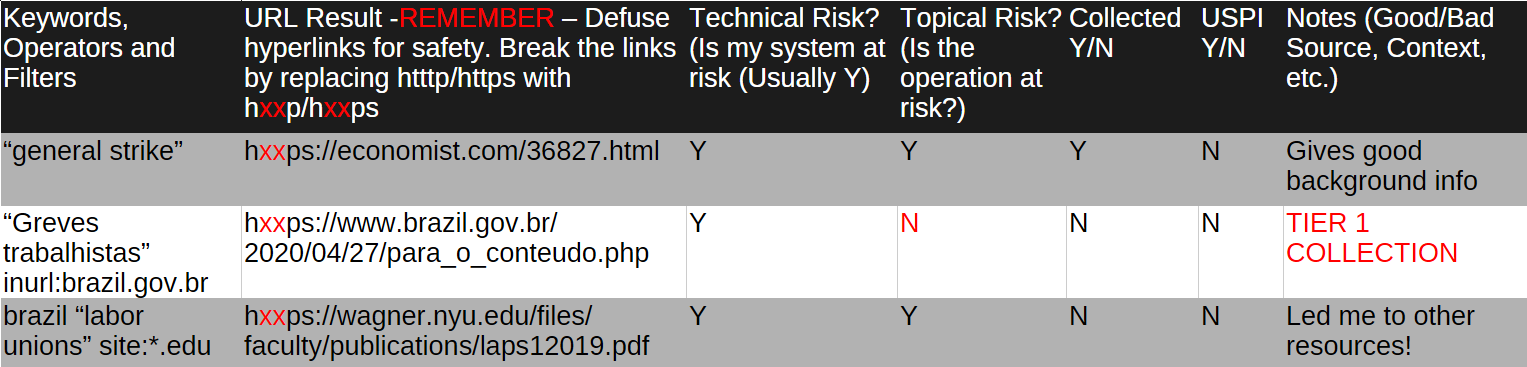
Publicly Available Information (PAI) (Step 1)
Information that is:
Published or broadcast for public consumption
Available on request to the public
Accessible online or otherwise to the public
Available to the public by subscription or purchase
Able to be seen or heard by any casual observer
Made available at a meeting open to the public
Obtained by visiting place/attending event open to the public